SAML Configuration for Portals Behind a URL Prefix
1. When is This Needed?
If user is deploying the CFX Portal behind a URL prefix (e.g., https://<domain>/aiops), it is important to explicitly set the strict flag to false in the SAML metadata configuration. This setting helps prevent invalid_destination errors that can occur due to URL rewrites by HAProxy or similar proxies.
2. Why is "strict": false Required?
With python3-saml version 1.16.0, the default value of strict is true unlike in older versions where it was false by default. Therefore, when hosting the portal behind a path prefix (such as /aiops), you must manually include as shown below in the configuration to ensure compatibility and prevent SAML validation issues.
3. Where to Configure
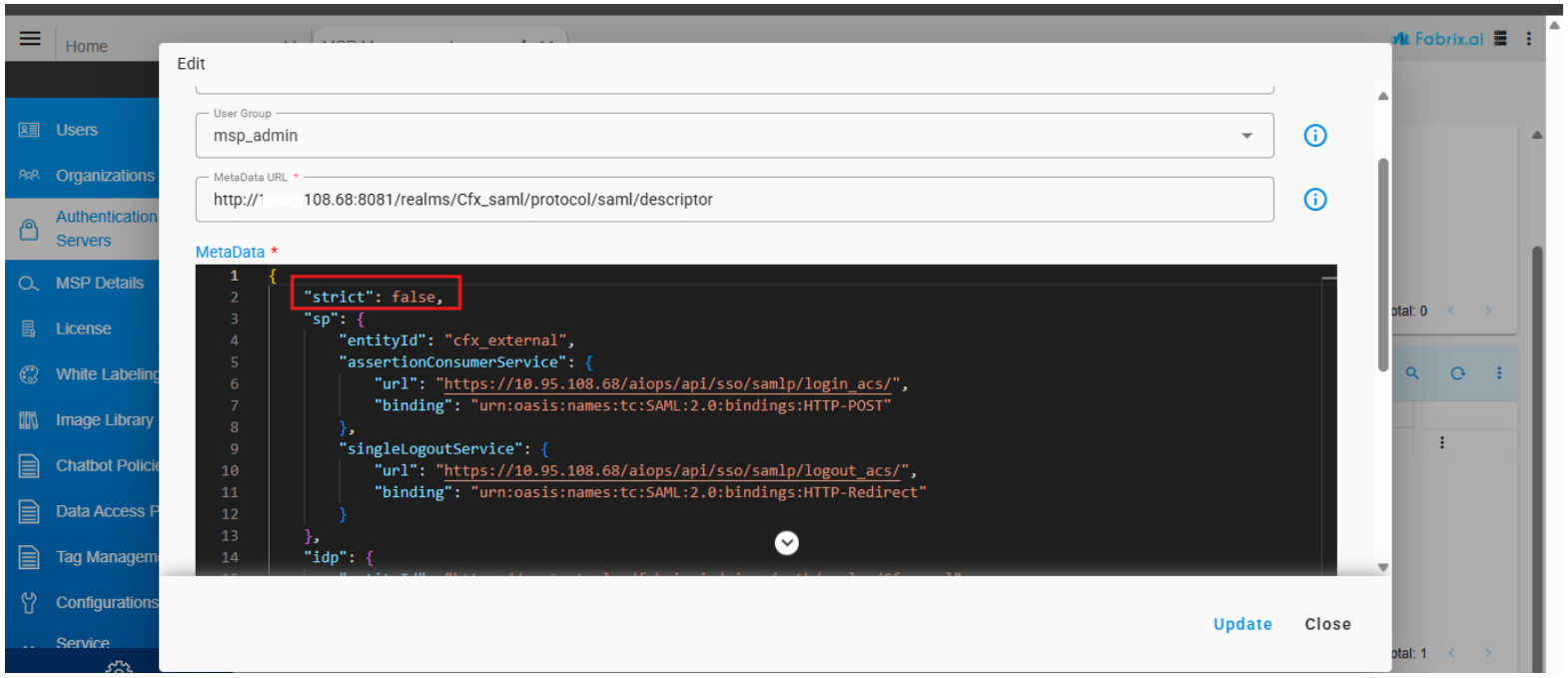
Navigation Path: Administration → Authentication Servers → SSO Details → Add or Edit (an existing saml configuration)
Action Required: Edit the configuration and add "strict": false, then save the changes.
{
"strict": false,
"sp": {
"entityId": "<client name>",
"assertionConsumerService": {
"url": "https://<domain>/aiops/api/sso/samlp/login_acs/",
"binding": "urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
},
"singleLogoutService": {
"url": "https://<domain>/aiops/api/sso/samlp/logout_acs/",
"binding": "urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect"
}
},
"idp": {
"entityId": "https://<idp-host>/realms/<realm_name>",
"singleSignOnService": {
"url": "https://<idp-host>/realms/<realm_name>/protocol/saml",
"binding": "urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect"
},
"singleLogoutService": {
"url": "https://<idp-host>/realms/<realm_name>/protocol/saml",
"binding": "urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect"
},
"x509cert": "<idp x509 cert here>"
}
}